Getting the Reports
Reports are generated as the result of a scan and contain all detected vulnerabilities and relevant information. The type of reports available depends on the Product used.
Confidentiality: reports may contain highly sensitive data about your network and servers. Do not share them with unauthorized individuals.
PCI Product Reports
For the PCI product, we provide the following report types:
- Attestation of Compliance (AoC): The Attestation of Scan Compliance provides an overall summary indicating whether the scan customer has met the necessary security compliance standards.
- Executive Summary: The Executive Summary provides a high-level overview of the scan results, including the number of vulnerabilities detected and their severity levels.
- Detailed Report: This report contains comprehensive information about all detected vulnerabilities and potential vulnerabilities. It includes detailed descriptions, affected software versions, CVE references, and recommended solutions to help mitigate the identified risks.
VRMS Product Reports
For the VRMS product, we provide the following report types:
- Vulnerability Assessment: A detailed report outlining all identified vulnerabilities, including their severity, affected systems, and recommended remediation steps.
- Executive VRMS: A high-level summary tailored for executive stakeholders, providing an overview of the vulnerability landscape without in-depth technical details.
- Vulnerability Summary: A concise report summarizing the key findings of a vulnerability scan, focusing on critical issues that require immediate attention.
Penetration Testing Reports
For the Penetration product, we provide the following report types:
- Executive Report: A high-level summary for stakeholders that provides an overview of penetration testing results, highlighting key security risks and recommendations.
- Penetration Report: This report presents the findings from a comprehensive penetration test, detailing vulnerabilities, exploited weaknesses, and in-depth security insights.
- Remediation Report (Excel file): This report includes a remediation detail workspace, a remediation summary, and an asset summary, helping teams effectively plan and track security fixes.
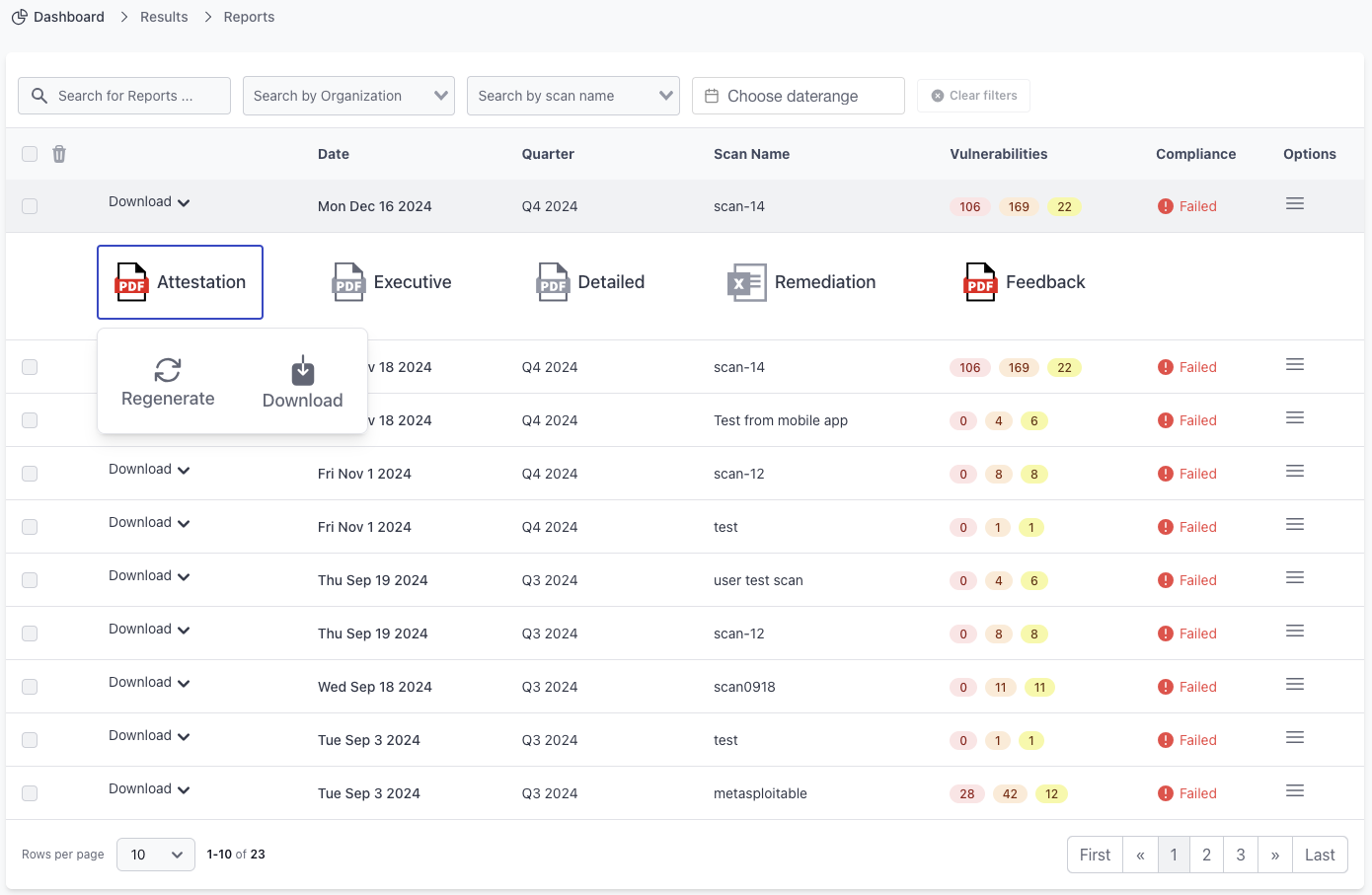
Generating and Downloading Reports
You can visit the Reports page from the menu and click on a report row to view the available report types. Then, you can click on Generate Report and wait for the PDF file to be generated. Once the report is ready, you can download it.
Retention Period: We retain reports and scan results for 3 years from the date the scan was completed. Ensure that you download and store the PDF report files if you need to keep them for a longer duration. After the retention period, the reports are automatically deleted from our system and cannot be recovered.
Report Generation Time: The time required to generate a report depends on the number of vulnerabilities found. Generally, reports are generated in under 10 seconds, but in some cases, it may take longer.
Additional Recommendations
- Regularly review and download reports after each scan to maintain a historical record of your security posture.
- Compare reports over time to track improvements and identify recurring security issues.
- Use executive reports for management-level reviews, while detailed reports should be used for technical security assessments and remediation planning.